الحوسبة الطرفية: تدمير الكمون في سوق عالمي
Executive Summary
In the elite tier of digital commerce, latency is not merely a technical metric; it is an architectural failure that shatters the illusion of exclusivity. Edge computing eradicates this friction, decentralizing infrastructure to execute complex processing within milliseconds of the end user, enforcing a paradigm where global scale and instantaneous response are no longer mutually exclusive.
The Physics of Delay: Diagnosing Centralized Architecture
Traditional enterprise architecture relies on a centralized topology. Compute clusters and monolithic databases are anchored in a handful of primary availability zones. While this model simplifies deployment, it inherently violates the demands of a globalized, high-net-worth user base. When a luxury consumer in Dubai requests a dynamic payload from an origin server in Virginia, the resulting Round Trip Time (RTT) is mathematically bottlenecked by the speed of light and BGP routing hops.

Architecting the Edge: Decentralized Proximity Processing
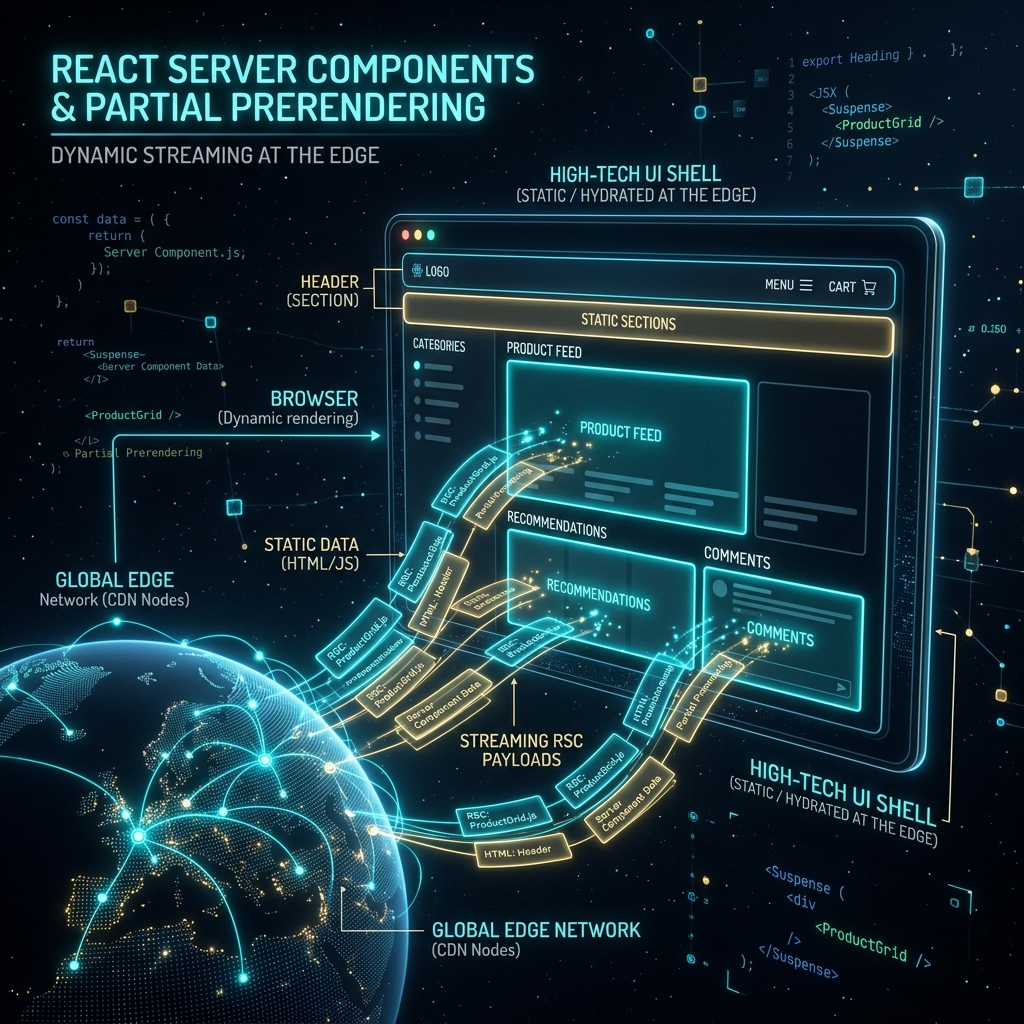
Edge computing dismantles the centralized origin model by distributing processing power directly to the network's perimeter. It places execution environments in globally dispersed Points of Presence (PoPs), ensuring that the physical distance between the user's device and the server is reduced from thousands of miles to mere blocks. Modern edge architecture pushes dynamic, server-side logic to the geographic perimeter.
Serverless Edge Functions and V8 Isolates
The technological leap that made edge computing viable is the transition to V8 isolates and WebAssembly (Wasm). Unlike heavy containers, isolates share a single runtime process, allowing microservices to execute in under 5 milliseconds. This enables dynamic authentication, personalization Manipulating the DOM, and API stitching at the nearest PoP, bypassing the origin entirely.
Distributed State and Globally Replicated Data
Executing code at the perimeter is useless if that code must query a centralized database. Strict edge performance requires globally distributed data primitives—edge-native key-value stores and globally replicated relational databases with read-replicas in every major region. By utilizing Conflict-free Replicated Data Types (CRDTs), systems guarantee low-latency reads locally while maintaining eventual consistency globally.
Hardening the Perimeter: Zero Trust and Edge Security
Moving execution logic to the edge alters an enterprise's security posture. By shifting the perimeter outward, malicious traffic is neutralized at the node closest to the attacker. Distributed WAF, bot mitigation, and DDoS scrubbing are executed concurrently with the user's request. This facilitates a strict Zero Trust model where the origin server is entirely obfuscated from the public internet.

Conclusion: Uncompromising Performance
At EVDOPES, our architectural philosophy dictates that technology must be invisible. The user must experience the brand, not the infrastructure. Edge computing is the structural mechanism that enforces this invisibility on a global scale. By leveraging decentralized compute and globally replicated state, we transform complex architectures into seamless, frictionless environments designed for silent, uncompromising conversion.